Leaked Document Appears to Show NSA Infiltrated Cryptos, Tor, VPN
 A photograph posted on imageboard 4chan appears to show a leaked 21 August 2017 memorandum from the US Army Cyber Protection Brigade. The document alludes to the US Army teaming with the National Security Administration (NSA) in ongoing successful investigations against “Tor, I2P, and VPN,” with a request for additional funding for further projects against cryptocurrencies. Also read: Nassim Nicholas Taleb vs David Birch on The Bitcoin Standard
A photograph posted on imageboard 4chan appears to show a leaked 21 August 2017 memorandum from the US Army Cyber Protection Brigade. The document alludes to the US Army teaming with the National Security Administration (NSA) in ongoing successful investigations against “Tor, I2P, and VPN,” with a request for additional funding for further projects against cryptocurrencies. Also read: Nassim Nicholas Taleb vs David Birch on The Bitcoin StandardLeaked Document Appears to Show Privacy Solutions Compromised
“The success we have had with Tor, I2P, and VPN,” begins a reportedly leaked picture of a memorandum on imageboard 4chan, complete with Department of Defense letterhead, appearing to be from the United States Army’s Cyber Protection Brigade “cannot be replicated with those currencies that do not rely on nodes. There is a growing trend in the employment of Stealth address and ring signatures that will require additional R&D.” It has been long assumed government military and law enforcement infiltrated and compromised aspects of The Onion Router (Tor), Invisible Internet Project (I2P), Virtual Private Networks (VPNs), and other ways of masking online activity, but confirmations were hard to come by.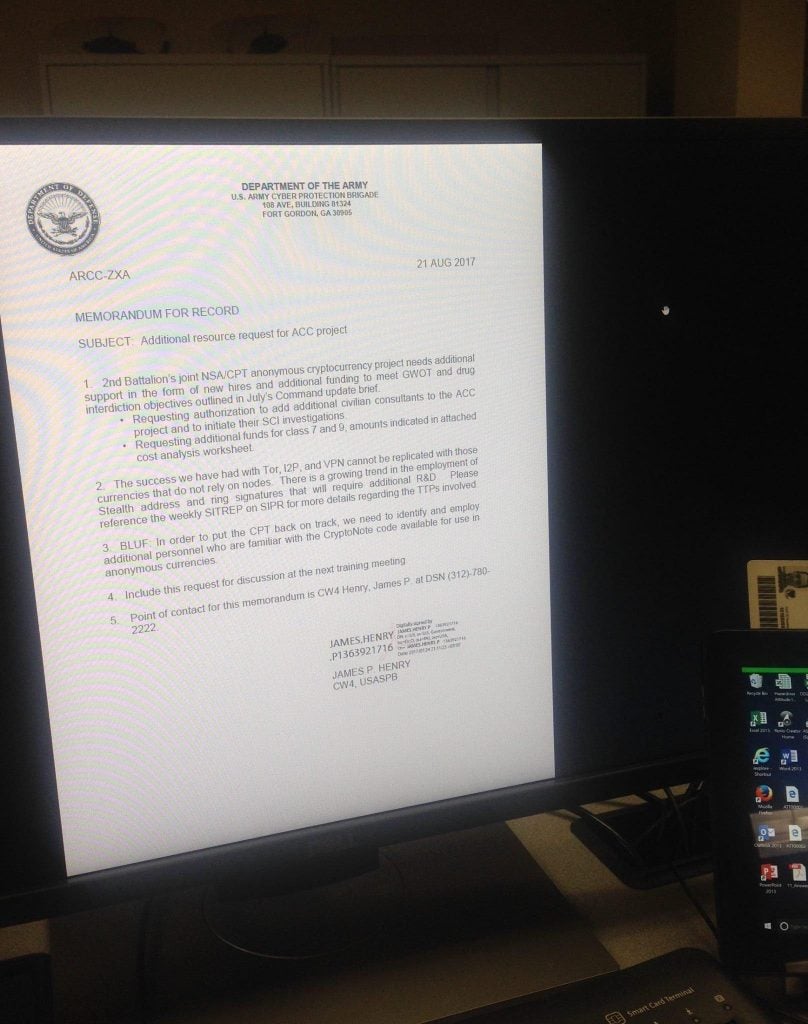 The picture in question appears to be legitimate, though a large dose of skepticism is always warranted in cases such as these. It isn’t always clear, either, why someone should wish this information be leaked. Nevertheless, the posted photograph shows an official looking document brought up on a terminal monitor, and just to the right is a Common Access Card or CAC, complete with picture, typical of a Department of Defense employee. In leaks, often easter eggs are left as a tell or clue. That’s not exactly apparent here, and it really could just be an instance of sloppiness. Another reasonable theory has to do with playing on the notorious fears of the crypto community, which at times can be easily sent into whips of cloak and dagger hysteria. A great way to limit usage of privacy solutions is to send out into the ecosystem rumors of their being anything but, a kind of Machiavellian version of spreading fear, uncertainty, doubt.
The picture in question appears to be legitimate, though a large dose of skepticism is always warranted in cases such as these. It isn’t always clear, either, why someone should wish this information be leaked. Nevertheless, the posted photograph shows an official looking document brought up on a terminal monitor, and just to the right is a Common Access Card or CAC, complete with picture, typical of a Department of Defense employee. In leaks, often easter eggs are left as a tell or clue. That’s not exactly apparent here, and it really could just be an instance of sloppiness. Another reasonable theory has to do with playing on the notorious fears of the crypto community, which at times can be easily sent into whips of cloak and dagger hysteria. A great way to limit usage of privacy solutions is to send out into the ecosystem rumors of their being anything but, a kind of Machiavellian version of spreading fear, uncertainty, doubt. 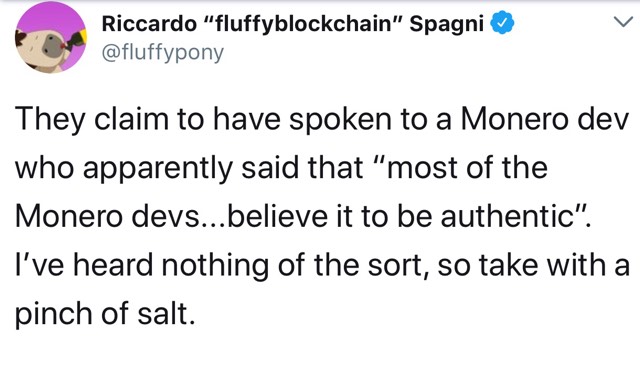
Old New News?
“2nd Battalion’s joint NSA/CPT anonymous cryptocurrency project needs additional support,” the memo’s first line reveals a unit involved with the National Security Administration (NSA) and Cyber Protection Team (CPT) urging more funding for “new hires and additional funding to meet GWOT and drug interdiction objectives outlined in July’s Command update brief,” Global War On Terror (GWOT) being a go-to pretext for nearly two decades of invasive military and law enforcement action. While outlets such as Deep Dot Web might claim to have broken news, the truth is the photograph was distributed among Steemit, Veekly, and even Warosu some five months ago. The document is still worth dissecting, assuming its legitimacy, if only for the last sentence: Bottom Line Up Front (BLUF), “In order to put the CPT back on track, we need to identify and employ additional personnel who are familiar with the Crypto Note code available for use in anonymous currencies,” the memo stressed. Crypto Note is the app layer for privacy tokens such as Bytecoin (BCN), Monero (XMR), Karbo (KRB), and Boolberry (BBR). Crypto Note bills itself as using a memory bound function which is difficult to pipeline. That the relevant agencies tasked with monitoring and tracking privacy internet solutions, and now coins, needs outside help with Crypto Note might speak volumes about where the various government divisions are in terms of their security acumen. For its part, Deep Dot Web claims to have contacted “a Monero developer, who spoke on condition of anonymity,” and the dev “said that most of the Monero developers who have seen the leak believe it to be authentic. Several sources who were formerly in the Army have also said they believe the document to be real. The contents of the document are completely plausible,” poster Dividedbyo stressed. “An anonymous source who is currently serving in the US Army said from what they understood, that the information contained in the document was accurate.” What do you make of this document? Is it real? Let us know in the comments section below.
Crypto Note is the app layer for privacy tokens such as Bytecoin (BCN), Monero (XMR), Karbo (KRB), and Boolberry (BBR). Crypto Note bills itself as using a memory bound function which is difficult to pipeline. That the relevant agencies tasked with monitoring and tracking privacy internet solutions, and now coins, needs outside help with Crypto Note might speak volumes about where the various government divisions are in terms of their security acumen. For its part, Deep Dot Web claims to have contacted “a Monero developer, who spoke on condition of anonymity,” and the dev “said that most of the Monero developers who have seen the leak believe it to be authentic. Several sources who were formerly in the Army have also said they believe the document to be real. The contents of the document are completely plausible,” poster Dividedbyo stressed. “An anonymous source who is currently serving in the US Army said from what they understood, that the information contained in the document was accurate.” What do you make of this document? Is it real? Let us know in the comments section below.Images courtesy of Pixabay, 4chan.
Not up to date on the news? Listen to This Week in Bitcoin, a podcast updated each Friday. The post Leaked Document Appears to Show NSA Infiltrated Cryptos, Tor, VPN appeared first on Bitcoin News.
Anonymity Boolberry (BBR) Bytecoin (BCN) Common Access Card Crypto Note Department of Defense Global War On Terror Invisible Internet Project (I2P) Karbo (KRB) Machiavellian Monero (XMR) N-Featured National Security Administration Privacy Steemit The Onion Router (Tor) United States Army’s Cyber Protection Brigade Veekly Virtual Private Networks (VPNs) Warosu



